If you use so-called ‘free’ Wi-Fi networks while at your favorite cafe or while traveling, you might get more than you bargained for. Protect yourself – and your identity – with these simple tips. You’re sitting in an airport lounge and seize the chance to check your e-mails before your flight departs. You log on and are tempted by a wireless Internet provider offering free Internet access. So, do you take it?
Security experts warn that hackers may be masquerading as free public Wi-Fi providers to gain access to the laptops of unsuspecting travelers. All it takes, they say, is a computer program downloaded from the Internet, an open access point and a user who has ignored basic security advice. The difficulty for travelers is differentiating between a good Internet access hotspot and a rogue, or somebody trying to actually glean credentials from you. The issue is that you don’t necessarily know the difference between a good and a bad one.
This could happen in a number of ways, but one of the sneakiest is a “rogue” Wi-Fi network that look like a free alternative to your hotel’s $10 to $15/day rate. In other words, tech-savvy thieves are taking advantage of your thirst for constant connectivity – and desire to save a few bucks.
The basic idea is someone in the vicinity has created a ‘free Wi-Fi network’ that you connect to, but in doing so, you’re allowing them to tap into your info, access your files and possibly steal your personal identity too. These rogue networks are really individuals who have software to hack into your systems — and because the majority of people’s laptops are not protected, they’re a lot more susceptible than they think.
In fact, a software tool has been developed that demonstrates the risk of unprotected wireless networks. This software tool acts as a promiscuous access point that masquerades itself as a wireless network. It makes the victim connect to our rogue wireless network automatically.
Rogue operators will often craft network names similar to the name of the hotel or the coffee shop where your end user is attempting to connect. One careless click and your data is exposed. Scary stuff. So, what to do? You’ve got your work cut out for you, and it starts with awareness, say the experts. So consider these following steps:
Whenever possible, avoid free public Wi-Fi networks. When a traveler goes to a hotel, they should make sure they have a wired [Ethernet] connection.
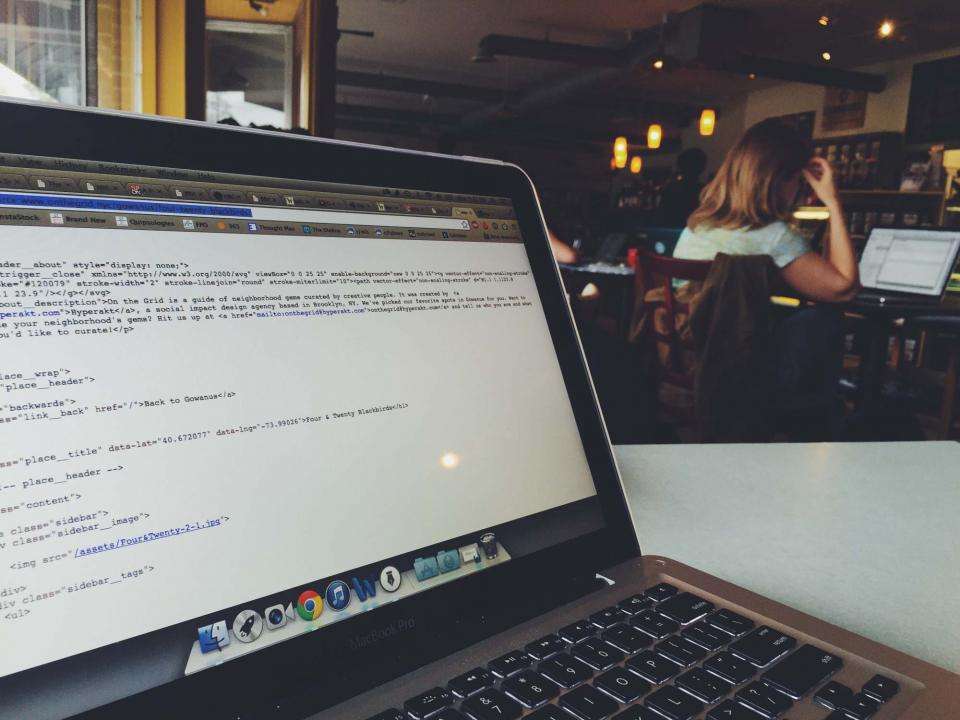
- Be efficient. If you can’t resist a free public Wi-Fi network, get on, get what you need and get off — and don’t do any financial things until you’re back at home. It also doesn’t hurt to ask the establishment (such as a coffee shop) if the “StarbucksFree123″ network is really theirs before logging on.
- Use VPN. Only use free public Wi-Fi if you have VPN (Virtual Private Network) access – otherwise, everything you do can be easily monitored by anyone nearby. Travelers should be aware that a new software program exists call “FireSheep” which can easily capture your passwords when you use public WiFi networks. Anyone with bad intentions capable of following a few simple online instructions can install a simple “Firesheep” Firefox plug-in, and then join an open wireless network nearby. Firesheep would then reveal who else is on that network that have visited unencrypted websites, which just so happens to include Facebook and Twitter, two of the most popular destinations on the web today. Firesheep is an extension for the Firefox browser that can grab your login credentials for sites such as Facebook and Twitter.
- BYOC (Bring Your Own Connection). Another option is to use WAN-enabled laptops, USB sticks with cellular connectivity or to create a mobile hotspot through your smartphone or tablet.
- Use security software. And make sure all security software is updated regularly, enable firewalls and even consider using tools to encrypt sensitive data (there are many free options available, too).
- Only through education, secured connections, and some common sense can you keep your personal and professional data safe from cyber-snoopers, waiting to attack through a free public Wi-Fi.